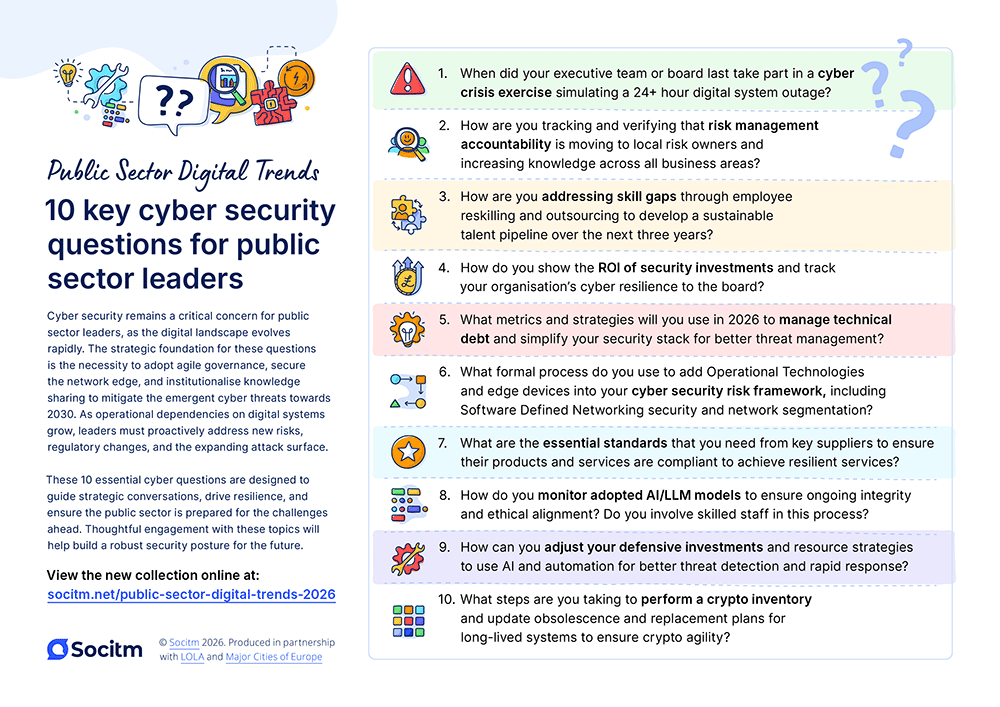
Cyber security remains a critical concern for public sector leaders, as the digital landscape evolves rapidly. The strategic foundation for these questions is the necessity to adopt agile governance, secure the network edge, and institutionalise knowledge sharing to mitigate the emergent cyber threats towards 2030.
As operational dependencies on digital systems grow, leaders must proactively address new risks, regulatory changes, and the expanding attack surface.
These 10 essential cyber questions are designed to guide strategic conversations, drive resilience, and ensure the public sector is prepared for the challenges ahead. Thoughtful engagement with these topics will help build a robust security posture for the future.
1. When did your executive team or board last take part in a cyber crisis exercise simulating a 24+ hour digital system outage?
Strategic rationale: Cyber incidents increasingly have significant operational impacts. Exercising with scary scenarios (Turning up the ‘Evil Dial to 11’) that involve senior leaders are essential to drive strategic security conversations, demonstrate commitment and build resilience.
2. How are you tracking and verifying that risk management accountability is moving to local risk owners and increasing knowledge across all business areas?
Strategic rationale: Governance frameworks must be agile. Regulatory updates (like NIS2 and CAF Version 4) are affecting more organisations. A principle-led approach requires embedding risk management into the organisation’s DNA, moving beyond checklist compliance.
3. How are you addressing skill gaps through employee reskilling and outsourcing to develop a sustainable talent pipeline over the next three years?
Strategic rationale: Staffing and resources will continue to be scarce. Forward planning and retention of key staff needs to be factored into organisation and risk assessments. Staff retention may require novel approaches, such as flexible working and additional training and development.
4. How do you show the ROI of security investments and track your organisation’s cyber resilience to the board?
Strategic rationale: Security leaders are under pressure to show return on investment. Utilising frameworks like the CAF helps articulate cyber security and resilience alignment against a set of desired outcomes. This necessitates improving cyber risk communication into clear, business-focused terms.
5. What metrics and strategies will you use in 2026 to manage technical debt and simplify your security stack for better threat management?
Strategic rationale: Technical debt (Legacy) is a significant drag on security and velocity, leading to operational risk. The objective should be to consolidate tools to extract greater value and enhance resilience
6. What formal process do you use to add Operational Technologies and edge devices into your cyber security risk framework, including Software Defined Networking security and network segmentation?
Strategic rationale: As we move forward, smart places and monitoring are getting more pervasive and necessary. This is adding a huge amount of data to the network. Cyber threats can start with the planning and deployment of these edge devices. These devices need to be incorporated into the overall cyber strategy, monitoring and assurance regime.
7. What are the essential standards that you need from key suppliers to ensure their products and services are compliant to achieve resilient services?
Strategic rationale: Robust third-party risk management is crucial, as the supply chain is a prime attack vector. Organisations must evaluate providers carefully, especially those outside assured lists (like the Assured Solutions List (ASL), who may prioritise commercial motives over security
8. How do you monitor adopted AI/LLM models to ensure ongoing integrity and ethical alignment? Do you involve skilled staff in this process?
Strategic rationale: The rise of generative AI introduces new vulnerabilities, such as prompt injection, and expands the attack surface across the entire AI lifecycle. Leaders must secure AI models as “data sealed computational files” to prevent external code interference, a key mitigation against emerging threats
9. How can you adjust your defensive investments and resource strategies to use AI and automation for better threat detection and rapid response?
Strategic rationale: AI is becoming embedded in cyber security products and services. Attackers are leveraging AI to undertake attacks and to revise and adapt their tactics in real time. Leaders need to ensure that their products and services are architected to be zero trust and secure by design.
10. What steps are you taking to perform a crypto inventory and update obsolescence and replacement plans for long-lived systems to ensure crypto agility?
Strategic rationale: The timeline for functional quantum computer cryptography is uncertain (5, 10, or 15 years), but preparatory work, such as building a cryptographic metadata database and planning the transition phase, must occur now. This has to start with basic cyber hygiene, ensuring obsolete cipher (encryption) suites (such as old versions of Transport Layer Security – TLS) are not allowed.